Your Data.
Under Your Control.
CIDNIC builds S3-compatible storage software and appliances for organizations that require security, governance, and operational ownership—without defaulting to a single public cloud control plane.

Enterprise Snapshot
An appliances-first object storage platform engineered for enterprise realities: procurement-ready deployments, predictable operations, and S3-compatible integration for modern workloads.
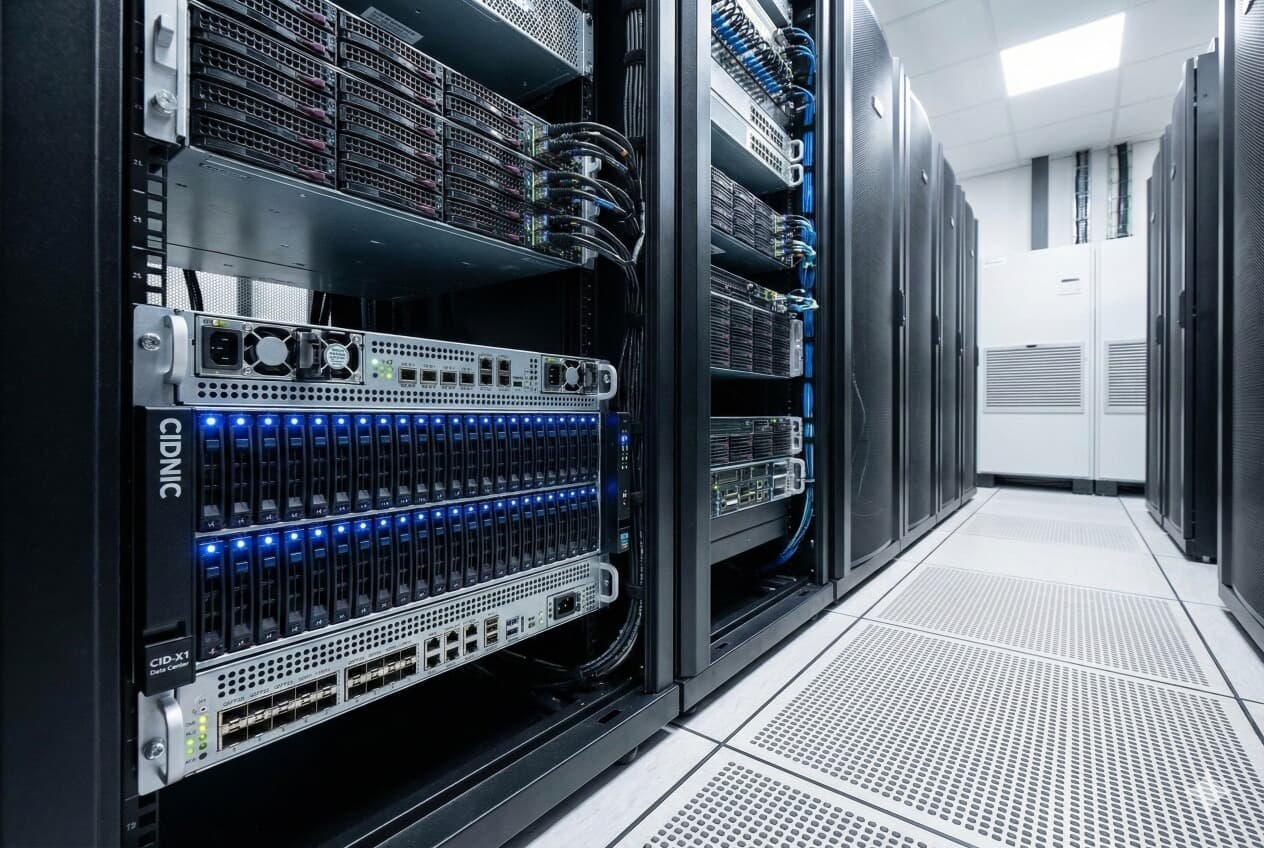
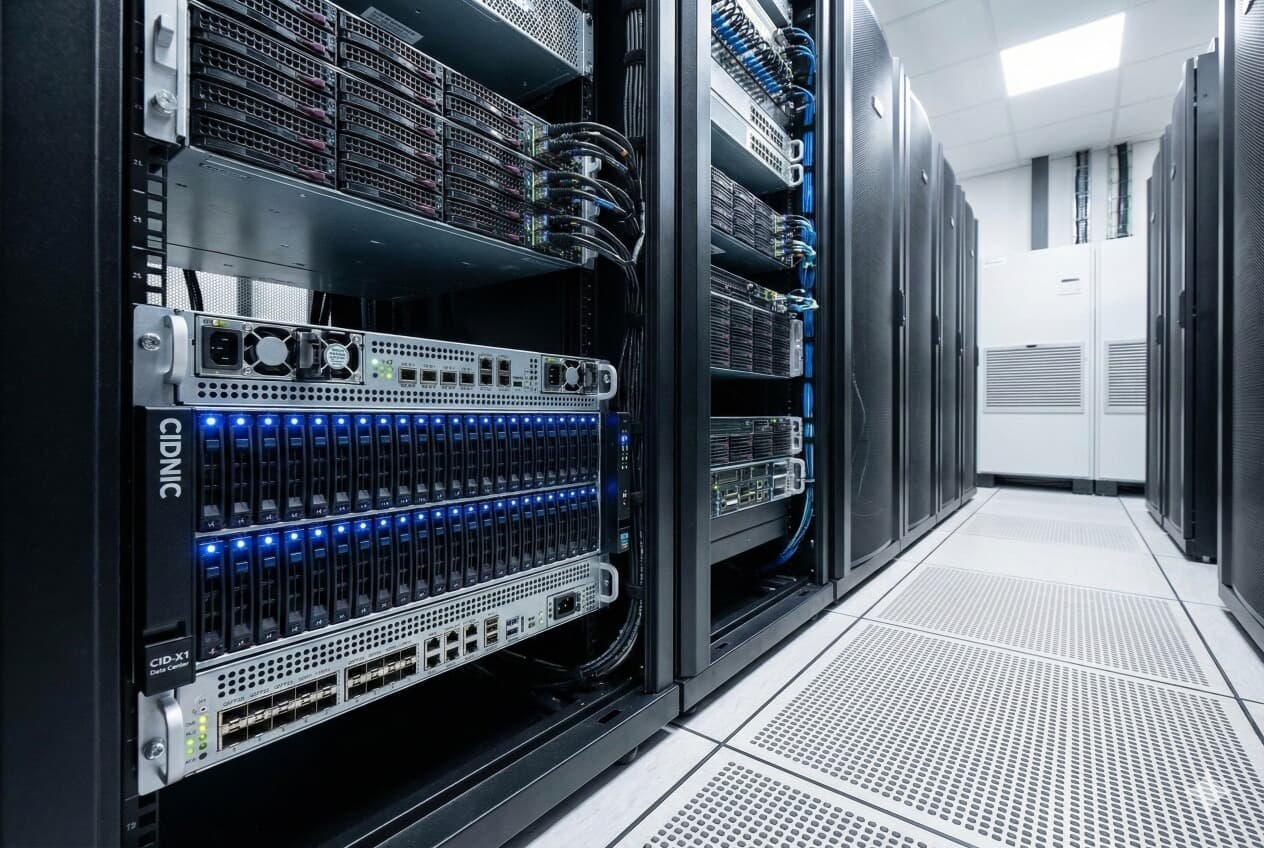
CID-X1 Data Center
High-density, enterprise storage appliance optimized for CIDOS Enterprise—built for predictable scale, resilient operations, and procurement-aligned deployments.
CIO / IT
Standardize on validated appliances for repeatable rollouts, then extend with software deployments where you need flexibility—without breaking S3 tooling or pipelines.
CISO / Security
Hardened controls for regulated data: TLS in transit, encryption at rest, RBAC, and immutable retention patterns with Object Lock (WORM) to strengthen ransomware posture.
Finance / Procurement
Procurement-friendly options with clear sizing inputs, support tiers, and a structured evaluation path—built for predictable budgeting and long-term operational ownership.
The Ecosystem
Start with appliances for standardized deployments, then extend with software editions and enterprise utilities—built to integrate with the tools your teams already use.
CID-XS Appliance
Compact edge and ROBO appliance for standardized remote deployments with the same S3-compatible workflow.
CIDOS Enterprise
Governance and resilience features for regulated environments—Object Lock (WORM), RBAC, replication, and enterprise support options.
Just Data Copier (JDC)
Enterprise-grade file transfer utility with resume, verification, tuning, and operational observability—designed to fit existing workflows.
CIDOS Community
A free entry point for developers and labs—S3-compatible on a single node to evaluate workflows before scaling.
Engineering with Principles
We don't chase trends. We build solid foundations for the next decade of data storage.
Sovereign by Design
Run storage on infrastructure you control. Telemetry is optional. Key management is designed for customer governance via LocalKMS and external KMS options.
Open Standards
We believe in avoiding vendor lock-in. While our engine is proprietary, we prioritize open API standards (S3) so your applications remain portable.
Privacy First
Privacy isn't a setting; it's architecture. From encryption-at-rest to strict access controls, we engineer for high-assurance environments.
Why CIDNIC?
What sets us apart from cloud storage providers and other on-premises solutions.
Complete Data Sovereignty
Your data, your encryption keys, your infrastructure. No data leaves your premises — ever. Zero telemetry by default.
Ransomware-Resilient by Design
Object Lock (WORM) prevents deletion even by compromised admin accounts. Auto-healing erasure coding recovers from disk failures without manual intervention.
Zero External Dependencies
Works 100% offline after one-time activation. No cloud control plane, no mandatory SaaS dependency, no internet required for operations.
Predictable Cost Model
One-time license, no per-GB fees, no egress charges, no API request costs. Break-even within 6–12 months versus public cloud.
Customer Testimonials
Hear from organizations that have deployed CIDOS Enterprise for their mission-critical storage.
"CIDOS Enterprise gave us complete control over our compliance data. With Object Lock and on-premises encryption, we passed our SBP audit in record time. The 100% data sovereignty is exactly what our regulators require."
"We deployed CID-XS at 12 clinic locations for PACS imaging. The edge-to-headquarters replication works seamlessly, and our radiologists see zero latency on local reads. Storage costs dropped 60% compared to our previous cloud setup."
"After a ransomware incident at a peer company, we fast-tracked our immutable backup strategy. CIDOS Object Lock gives us WORM-protected backups that no one — not even a compromised admin — can delete. Recovery is minutes, not days."
Product Lineup
CIDNIC’s CIDOS platform delivers Amazon S3 API–compatible object storage for organizations that need predictable performance, strong governance controls, and deployment flexibility across edge and data center environments.
Choose the model that matches your operating requirements: software editions for integration into existing infrastructure and automation, or turnkey hardware appliances for standardized procurement, repeatable rollouts, and consistent operations.
- Application portability with S3 API compatibility
- Governance controls such as RBAC (Role-Based Access Control)
- Immutability options like Object Lock with WORM (Write Once, Read Many)
- Edge and ROBO (Remote Office / Branch Office) deployment support
Hardware Appliances

CID-XS Appliance
Edge & ROBO
Compact, quiet, and powerful. Designed for remote offices and edge computing where space is at a premium but reliability is non-negotiable.
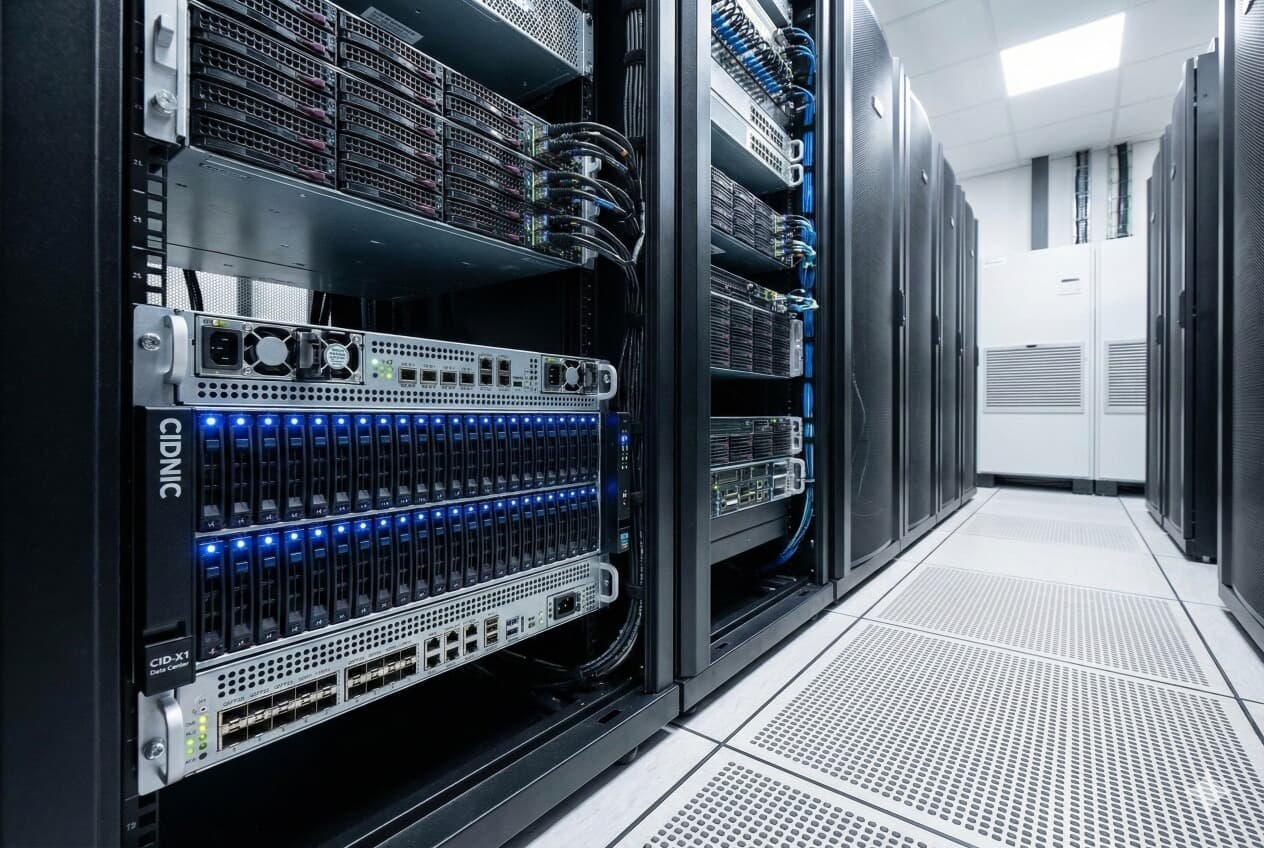
CID-X1 Data Center
Data Center Series
High-density 4U rackmount storage server. Massive capacity, dual-redundant architecture, and NVMe acceleration for enterprise workloads.
Software Editions
CIDOS Community
Free Forever
The entry point to our technology. Perfect for developers, home labs, and single-node workloads. Full S3 compatibility included.
CIDOS Enterprise
Commercial License
For regulated and mission-critical environments. Includes data scrubbing, disk remapping, Object Lock (WORM), RBAC, multi-site replication, and enterprise support options.
Enterprise Utilities
Just Data Copier (JDC)
Free Enterprise Utility
A high-performance, enterprise-grade network file transfer utility designed for mission-critical environments. Features adaptive network optimization, resume capability, and smart hash verification.
Just Data Copier
Free UtilityHigh-performance, enterprise-grade network file transfer utility designed for mission-critical environments.
Technical Specifications
- License MIT / Free
- Throughput Optimized Parallel Processing (2TB+ chunks)
- Security TLS/SSL Encryption + Token Auth
- Integrity Smart Hash (Auto MD5 / BLAKE2b)
- Observability Prometheus Metrics + Health Checks
Download Now
Single binary. No dependencies.
Docker Pull:
Key Features
Smart Hash Verification
Auto-selects optimized hashing for large files (e.g., BLAKE2b) to improve verification efficiency in real-world transfer workloads.
Resilient Resume
Chunk-level resume helps avoid restarting large transfers from scratch after interruptions.
Adaptive Network
Real-time profiling of RTT and packet loss to automatically tune window sizes.
Batch Processing
Supports wildcard patterns for mass transfer of logs, backups, and data sets.
Use Cases
Enterprise Benefits (Built to Fit Existing Workflows)
JDC is a single-binary utility designed to drop into established runbooks and automation. Use it interactively for first-time setup, or run it headless with flags/YAML for repeatable transfers.
- Single binary; no runtime dependencies
- CLI flags + YAML configuration (flags override config)
- Dry-run mode to validate changes before production
Move files from MB to TB+ efficiently with parallel chunking, resumable transfers, and optional verification. Adaptive network tuning helps sustain throughput across diverse network conditions.
- Chunk-level resume with integrity checks
- Optional hash verification (disabled by default)
- Adaptive tuning based on RTT (round-trip time) and packet loss
Quick Start (Client / Server)
Run JDC as a receiver on the target host, specifying an output directory and (optionally) a listen address/port.
Send from client to server over the network. Use optional compression where it makes sense for your data types and link.
Interactive setup walks you through mode selection, performance presets, and security options.
Configuration, Batch Transfers, and Change Control
Generate templates, review settings in version control, and reuse consistent transfer profiles across teams and environments.
Move sets of files using comma-separated lists or wildcards—ideal for logs, daily backups, and staged migrations.
Validate configuration and workflow changes without actual file I/O—useful for approvals and change windows.
Security, Verification, and Performance Tuning
- TLS/SSL encryption with token authentication
- Path validation to help prevent directory traversal
- Privacy-focused logging (no sensitive paths or hash values)
- Resource limits: connections, memory, and bandwidth controls
Hash verification is disabled by default. When enabled, JDC negotiates an optimized algorithm (MD5 for <50GB; BLAKE2b for ≥50GB).
Observability (Prometheus Metrics + Health Endpoints)
JDC exposes Prometheus-compatible metrics and Kubernetes-style health endpoints so operations teams can monitor throughput, error rates, resource usage, and service readiness without custom instrumentation.
bytes, duration, active transfers
latency, bandwidth, errors
memory, connections, open files
Common Options (Operational Cheatsheet)
Enable optional hash verification (client and server).
Compression with file-type awareness.
Parallelism (default: ~half CPU cores).
Transfer chunking and buffering controls.
Adaptive network optimization (RTT/packet loss).
Validate configuration without file I/O.
CIDOS Community Edition
Distributed object storage for single-node deployments.
Specifications
- License Free Community License
- Max Nodes 1 (Single Server)
- Erasure Coding Fixed (8+4)
- Encryption Standard (AES-256)
- Support Community Forums
Included Features
Get Started
Deploy in seconds using Docker.
-v /data:/data \
cidnic/cidos:latest server /data
CIDOS Enterprise
FlagshipEnterprise-grade object storage for regulated and mission-critical environments. Run S3-compatible storage with security, durability, and operational control.
Why CIDOS Enterprise?
CIDOS Enterprise is built for organizations that require secure, sovereign, S3-compatible storage with an operational model suitable for regulated and mission-critical environments.
Zero Trust Architecture
CIDOS Enterprise is built on Zero Trust principles — no implicit trust is granted to any user, device, or network. Every request is authenticated, authorized, and encrypted regardless of origin.
Verify Every Request
AWS SigV4 authentication signs every API request. No anonymous access by default — every operation carries a verified identity.
Least Privilege Access
Fine-grained IAM policies with 5,000+ users, 300+ groups, and 1,000+ roles. Grant only the minimum permissions required for each task.
Encrypt Everything
AES-256-GCM envelope encryption at rest. TLS 1.3 in transit. Metadata files encrypted separately. No unprotected data paths.
Continuous Auditing
25+ structured audit event types log every data access, auth event, encryption operation, and admin action with full trace correlation.
Network Micro-Segmentation
Bucket policies with condition-based access (IP CIDR, TLS, MFA). S3 Access Points for per-application network controls.
Temporary Credentials
STS (Security Token Service) issues short-lived credentials (15 min to 12 hours). MFA enforcement for sensitive operations.
CIDOS Enterprise implements defense-in-depth: encryption at every layer, identity verification on every request, and comprehensive audit trails across all operations. Security is not an add-on — it is foundational.
Enterprise Specifications
- Reliability Engine Data Scrubber + Disk Remapping
- Ransomware Protection Object Lock (WORM)
- Security RBAC + AD/LDAP Integration
- Encryption AES-256-GCM + External KMS
- Replication Active-Active Multi-Site
- Fault Tolerance 8+4 Erasure Coding (4-Disk Failure)
- CLI Management Server-Side Operations
- API Compatibility S3 v4 Signature + Presigned URLs
- Support Enterprise Support Options
Enterprise Use Cases
CIDOS Enterprise addresses data storage challenges across industries where security, compliance, and operational independence are non-negotiable.
Ransomware-Resilient Backup
Object Lock (WORM) ensures backup data cannot be deleted or encrypted by ransomware. Erasure coding auto-heals corrupted shards. Version rollback restores pre-attack state.
Banking & Financial Compliance
Store transaction records, audit logs, and compliance archives on-premises with AES-256 encryption and Object Lock retention. Meet SBP data localization and PCI-DSS audit requirements.
Healthcare & Medical Imaging
S3-compatible PACS/DICOM integration for medical imaging. Per-object encryption protects patient records. Edge deployment at clinics with central replication to hospital data centers.
Government & Public Sector
Fully air-gapped deployment with zero internet dependency. Data sovereignty controls keep all data, keys, and administration within national boundaries. Long-term archival with intelligent tiering.
Manufacturing & IoT
Edge deployment with full offline capability for factory floors. Multi-tenant isolation for plant/site segregation. Rate limiting and circuit breaker for resilient operations under load.
IT & SaaS Backend Storage
S3-compatible backend for SaaS applications with multi-tenant namespace isolation. CI/CD artifact storage with lifecycle auto-expiration. Eliminate per-GB and egress fees at scale.
Strategic Business Benefits
Enhanced Security
AES-256-GCM encryption, full IAM with MFA, and SigV4 authentication on every request. Defense-in-depth security that meets SOC 2, HIPAA, and PCI-DSS requirements.
Benefit: Reduced breach probability and blast radius.
Simplified Management
Two binaries, one YAML config, and a modern web console. No multi-component stack. Deploy in 30 minutes. Manage via browser or CLI — your choice.
Benefit: IT teams operational within 1-2 days.
Scalability
Start with a single server, add disks for capacity, add nodes for distribution. Scale from departmental to petabyte-scale without application changes or new tools.
Benefit: Pay for what you need today, grow when ready.
Ransomware Resilience
Object Lock (WORM) with Governance and Compliance modes. Legal Hold for litigation. Auto-healing with erasure coding. Immutable retention that survives credential compromise.
Benefit: Recovery in minutes, not days or weeks.
Data Sovereignty
All data, encryption keys, and administration stay on your infrastructure. No data sent abroad. Customer-controlled KMS with three backend options (Local, AWS KMS, HashiCorp Vault).
Benefit: Full regulatory compliance for data residency mandates.
Operational Independence
No external control plane, no mandatory SaaS dependency, no internet required after activation. Works in air-gapped, edge, and restricted environments.
Benefit: Resilience to external outages and connectivity disruptions.
Enterprise Observability
90+ Prometheus metrics, OpenTelemetry distributed tracing, P50/P95/P99 latency tracking, real-time alert rules engine with webhook notifications.
Benefit: Proactive management and rapid troubleshooting.
S3 Compatibility
Full AWS S3 API compatibility. Drop-in replacement — works with all S3 SDKs, CLI tools, and applications without code changes. Zero vendor lock-in.
Benefit: No application rewrites. Seamless migration.
Cost Predictability
No per-GB fees, no API request charges, no egress fees. One-time license with locally procured hardware. PKR cost structure eliminates USD exchange rate risk.
Benefit: Break-even within 6-12 months vs. cloud.
Integration Capabilities
CIDOS Enterprise integrates seamlessly with your existing enterprise tools and security infrastructure through standard protocols and APIs.
SIEM Integration
25+ structured JSON audit event types compatible with leading SIEM platforms for centralized security monitoring and threat detection.
IAM & Identity Providers
Full AWS IAM-compatible identity management with SigV4 authentication, STS temporary credentials, and MFA enforcement for privileged operations.
Endpoint & Backup Tools
Works as an S3-compatible backup target for enterprise backup and endpoint protection platforms. One-line config change to point to CIDOS.
Monitoring & Observability
90+ Prometheus metrics, OpenTelemetry distributed tracing with adaptive sampling, and pre-built Grafana dashboards for operational visibility.
Key Management Systems
Three KMS backend options for envelope encryption key management. Customer controls where and how encryption keys are stored and rotated.
DevOps & Development
S3 API compatibility means all standard SDKs and dev tools work without modification. Docker image under 80 MB for containerized deployments.
Total Cost of Ownership Estimator
Use your numbers. Defaults below are examples—edit for your environment.
Have Questions About CIDOS Enterprise?
Common questions about security, compliance, pricing, deployment, and more — answered in plain language.
CIDOS is a secure storage system for your company — much smarter and safer than a normal hard drive. It ensures nobody unauthorized can see your files (encryption), your files are safe even if drives break (erasure coding), you have a complete record of who touched what (audit trail), and your data stays on your own servers — not abroad.
It works like Amazon S3, so any software that works with S3 will work with CIDOS — no changes needed.
CIDOS has multiple layers of security:
- Encryption (AES-256-GCM): Every file is encrypted with military-grade standards. Even if someone steals a hard drive, they see only scrambled data.
- Access Control (IAM): Every user gets their own credentials. You control exactly who can see what.
- SigV4 Authentication: Every request is signed with a secure signature.
- MFA Support: Optional multi-factor authentication for extra security.
- Audit Trail: CIDOS logs everything — who accessed what, when, from which IP address.
- Credential Redaction: Passwords and secret keys are automatically hidden in logs.
Before an attack: Object Lock (WORM) makes important files undeletable. Least Privilege Access limits blast radius.
During an attack: Audit trails show exactly which files were accessed. Circuit Breaker limits abnormal operations.
After an attack: Auto-Healing rebuilds corrupted files from redundant copies. Version Rollback restores pre-attack state. Immutable backups survive because they simply cannot be modified.
Recovery time: Minutes to hours, not days or weeks.
YOU control the encryption keys. CIDOS gives you three options: Local KMS (keys on your server), AWS KMS, or HashiCorp Vault.
CIDNIC Systems does NOT have access to your data or encryption keys. The keys are generated and stored on YOUR infrastructure. We cannot see, read, or decrypt your data.
Yes, 100%. CIDOS runs entirely on your own servers in Pakistan. Data stored in Pakistan, encryption keys in Pakistan, administration done from Pakistan, audit logs in Pakistan — no data sent abroad.
This makes you compliant with SBP data localization requirements, the Personal Data Protection Bill, and internal data residency policies.
Yes. CIDOS addresses key SBP requirements: data resides in Pakistan on local servers, AES-256 encryption at rest and in transit, full IAM with 25+ audit event types, Object Lock for record retention (1-year, 7-year, etc.), and security incident detection via comprehensive audit trails.
Compliance evidence is recorded automatically, 24/7 — no manual collection before inspections.
No. After initial one-time license activation, CIDOS works 100% without internet. This is critical for organizations with unreliable internet, restricted networks, air-gapped environments, or locations affected by connectivity disruptions.
If your software works with Amazon S3, it works with CIDOS — no changes needed. This includes backup tools (Veeam, Commvault, Rclone), ERP systems (SAP, Oracle), database backups, DevOps tools (AWS CLI, boto3), file browsers (S3 Browser, Cyberduck), medical imaging (PACS/DICOM), data analytics (Spark, Jupyter), and AI/ML tools (TensorFlow, PyTorch).
Connection is simple: point your S3 endpoint URL to your CIDOS server instead of s3.amazonaws.com — typically a 1-line configuration change.
Nothing visible happens to your users — applications continue normally. CIDOS stores data across 12 disks using erasure coding (8 data + 4 parity). Even if 4 disks fail simultaneously, your data is 100% safe and accessible. When you replace a failed disk, CIDOS automatically detects the new disk and rebuilds all missing data — no manual intervention needed.
Simple and transparent: one-time license per machine with lifetime validity. No monthly subscriptions, no per-GB charges, no per-request charges, no egress fees. Everything is included — encryption, audit, monitoring.
For evaluation: Developer mode (all features, no license) and Trial mode (limited features, no cost) let you test before buying.
Quick evaluation: 30 minutes. Development/staging: 15 minutes. Production single-server (12 disks, encryption, full config): 2-4 hours. Multi-server cluster: 1 day.
CIDOS is just two files (server binary and CLI tool) plus one configuration file. No complex multi-component installation.
Six key reasons:
- Your data stays in your hands — on your servers, in your building, not abroad.
- Ransomware protection — locked files cannot be deleted or encrypted by attackers.
- Cost savings — one-time license, no monthly bills, no egress or API fees.
- Works without internet — critical advantage during connectivity disruptions.
- Regulatory compliance — automatic audit trails for SBP, SECP, and other regulators.
- No vendor dependency — you own the hardware and software license.
CIDOS Enterprise Partner Program
Join the CIDNIC partner ecosystem to deliver sovereign, enterprise-grade storage solutions to your customers.
System Integrators
Deploy CIDOS Enterprise as part of your infrastructure solutions. Offer deployment, configuration, and managed services to enterprise customers.
Value-Added Resellers
Bundle CIDOS with hardware solutions for turnkey storage appliances. Offer pre-configured, enterprise-ready storage to your customer base.
Technology Partners
Integrate CIDOS into your software platform as the storage backend. Offer S3-compatible storage with sovereignty controls to your end users.
Partner Benefits
Architecture guidance, deployment support, and technical training for your engineering team.
Approved collateral, co-branded materials, and joint go-to-market strategies.
Structured deal registration process with margin protection for qualified opportunities.
Dedicated partner support with severity-based response SLAs and escalation paths.
Engagement Process
Enterprise Adoption Path
Designed for enterprise evaluation and rollout: align stakeholders, validate fit, and deploy with predictable operational ownership.
Talk to Sales
Custom pricing based on capacity.

CID-XS Appliance
Edge ReadyHigh-performance edge storage designed for remote offices, branch locations, and distributed operations.
The CID-XS is engineered for "Store at the Edge" workflows. Perfect for retail locations, branch offices, manufacturing floors, or any distributed environment where you need local S3 storage with enterprise-grade reliability that seamlessly replicates to headquarters or cloud.
Why Purchase CID-XS?
- Eliminate WAN Dependency: Local storage means operations continue during internet outages
- Reduce Cloud Costs: Stop paying egress fees—only sync deltas to cloud
- Turnkey Deployment: Pre-configured CIDOS Enterprise—just power on and provision
- Compact Footprint: Fits in IT closets with limited space—no rack required
Hardware Specifications
CID-XS Use Cases & Benefits
Retail: Point-of-Sale Transaction Storage
Scenario: Stores and branches need local capture for POS, operational files, or video—without being blocked by WAN outages.
CID-XS Solution: Each store gets a CID-XS that caches transactions locally and auto-syncs to headquarters when bandwidth is available. Stores remain operational during WAN failures.
Manufacturing: Factory Floor Data Collection
Scenario: A site needs to ingest high-volume data locally for immediate processing while syncing selected data upstream.
CID-XS Solution: Installed on factory floor, CID-XS ingests microscope images via S3 API. ML pipelines analyze images locally with <10ms latency. Archive to HQ nightly.
Healthcare: Medical Imaging at Clinics
Scenario: Clinics and remote teams need fast local access to large files while maintaining centralized governance.
CID-XS Solution: Each clinic's PACS system writes DICOM images to CID-XS. Encrypted at rest (AES-256). Replicates to central hospital data center for long-term archive.
Oil & Gas: Remote Site Operations
Scenario: Remote sites ingest data continuously but have intermittent or expensive connectivity.
CID-XS Solution: CID-XS buffers data locally during offline periods. When satellite link is up, automatically syncs critical alerts first, then historical data—all compressed and encrypted.
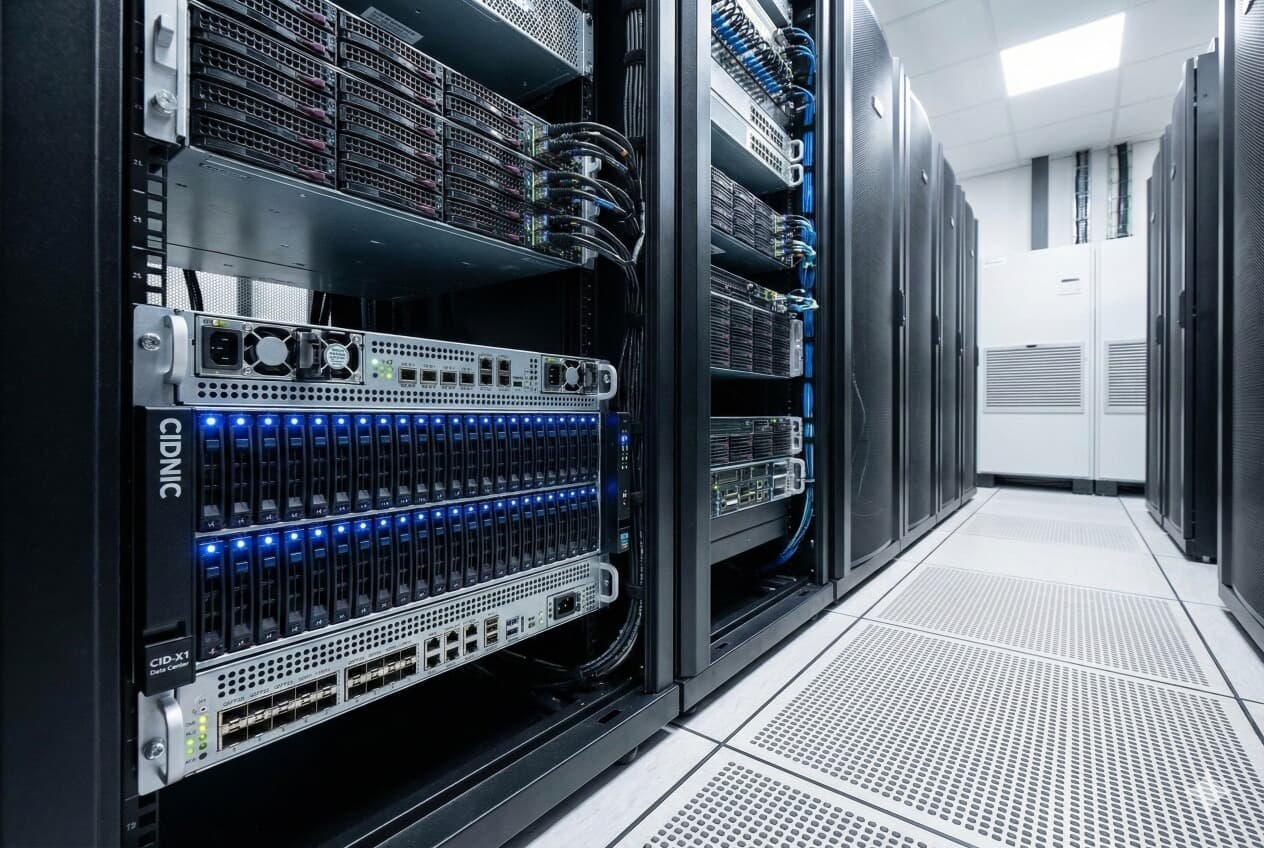
CID-X1 Data Center
Petabyte-scale density.
The CID-X1 is our flagship high-density storage server. Optimized for the CIDOS erasure coding engine (8+4), it delivers maximum durability with minimal overhead.
Hardware Specifications
Enterprise-Ready Options
Available with CIDOS Enterprise pre-installed and support plans aligned to your operational requirements.
Security & Governance
Designed for sensitive data with encryption at rest, TLS in transit, and S3-compatible controls including Object Lock (WORM) for immutable retention workflows.
Durability at Scale
Optimized for erasure coding (8+4) with resilience features like auto-heal and degraded-mode behavior—built for environments where data must stay online.
Operations-First
Fits into standard S3 tooling and enterprise workflows. Control provisioning, access, and lifecycle policies without forcing application rewrites.
Enterprise Use Cases
CID-X1 combines high-density enterprise hardware with CIDOS’s S3 (Amazon Simple Storage Service) API–compatible object storage to help teams control cost, reduce operational risk, and modernize data workflows without forcing application rewrites. Below are the most common ways organizations deploy CID-X1 in regulated and mission-critical environments.
Keep data on-prem to avoid unpredictable public-cloud egress and tiering fees while still using S3-native workflows.
- High density per rack unit to optimize space and power planning
- Standardized platform reduces integration and lifecycle complexity
- Predictable procurement and capacity expansion model
Design for ransomware resilience, retention requirements, and business continuity—without depending on a single external control plane.
- Object Lock with WORM (Write Once, Read Many) retention workflows
- Encryption at rest and TLS in transit for sensitive datasets
- Replication options to support DR (Disaster Recovery) readiness
Turnkey hardware simplifies deployment and accelerates adoption across multiple teams and business units.
- Validated appliance approach for repeatable rollouts
- Support plans aligned to operational requirements
- Accelerates consolidation of file, backup, and archive workflows
Adopt object storage using existing S3 tools, SDKs, and backup applications—minimizing change management.
- S3 API compatibility for common enterprise tooling
- RBAC (Role-Based Access Control) for multi-team governance
- Lifecycle and policy-driven controls for predictable operations
High-density architecture and high-bandwidth networking are designed for sustained ingest and large-object workloads.
- 4× 100GbE connectivity for data center-scale pipelines
- ECC memory and redundant power for reliability
- Erasure coding (8+4) optimized for durability with reduced overhead
Deploy in enterprise patterns with observability, automation, and resilience expectations built into the design.
- Multi-site replication for continuity and DR workflows
- Auto-heal and degraded-mode behavior for resilience under failure
- Operational utilities such as data scrubbing and disk remapping (Enterprise)
Use Object Lock with WORM retention to help prevent backup deletion or overwrite, while keeping vaults on-prem and compatible with S3-aware backup tooling.
- Immutable retention policies to support audit and recovery goals
- Segmentation and access control using RBAC
Centralize unstructured data for analytics pipelines and AI training sets with predictable performance, on-prem governance, and simplified data sharing across teams.
- High-throughput ingest for large-object and batch workloads
- Policy-driven access patterns for multi-tenant environments
Replicate between data centers to support archive durability and DR (Disaster Recovery) objectives, keeping critical datasets accessible even during partial site outages.
- Cross-site replication for continuity planning
- Supports staged recovery workflows and controlled rehydration
Implement retention, immutability, and audit-friendly controls for regulated data without relying on a single public cloud provider for policy enforcement.
- Encryption, TLS, and governance controls for sensitive workloads
- Retention policies aligned to internal and regulatory requirements
CIDOS Core
High-performance, distributed object storage compatible with Amazon S3 APIs.
Performance varies by hardware, network, drive/media type, and workload. Contact us for sizing guidance.
What is CIDOS?
CIDOS is a high-performance, S3-compatible object storage platform engineered for organizations that require data sovereignty, enterprise-grade security, and operational independence. It runs entirely on your own infrastructure — no external control plane, no mandatory cloud dependency.
Available as software (Community and Enterprise editions) and pre-configured hardware appliances (CID-XS and CID-X1), CIDOS covers use cases from single-node developer workloads to petabyte-scale distributed deployments.
Data Sovereignty
All data, keys, and administration stay on your infrastructure. Zero telemetry by default.
Air-Gapped Ready
Works 100% offline after one-time activation. No internet required for operations.
Self-Healing
Automatic data scrubbing, erasure coding repair, and disk remapping without manual intervention.
S3 Compatible
Drop-in replacement for AWS S3. Works with all S3 SDKs, CLI tools, and applications.
Deployment Flexibility
Choose the deployment model that fits your operational requirements — from a developer laptop to a multi-site distributed cluster.
Developer
Single binary, no license. Full feature access for evaluation and development.
Single Server
Production deployment with 12 disks. Erasure coding (8+4) for 4-disk failure tolerance.
Distributed
Multi-node cluster for capacity scaling and load distribution across servers.
Multi-Site
Active-active replication across data centers for disaster recovery and business continuity.
Enterprise Security & Compliance
Ransomware Protection
Object Lock (WORM): Make your data immutable. Write Once, Read Many protection ensures that backup data cannot be deleted or overwritten by ransomware or malicious actors for a set retention period.
S3 Object Lock CompatibleAdvanced Encryption
AES-256-GCM envelope encryption is standard. We support external Key Management Systems (KMS) for centralized control.
- Native Local Key Vault
- HashiCorp Vault Integration
- AWS KMS Support
Identity & Access (RBAC)
Granular Role-Based Access Control allows you to define precise permissions. Integrate with your existing LDAP/AD providers for seamless authentication.
POLICY: Allow s3:PutObject on /finance/*Data Management & Multi-Cloud
Lifecycle Management
Automate your data cost optimization. Set policies to automatically transition older data to cheaper storage tiers or expire data after a set retention period to meet compliance (GDPR/HIPAA).
Active Replication
Ensure high availability with async active-active replication. Replicate buckets across different racks, data centers, or geographic regions for disaster recovery.
Multi-Cloud Tiering
Don't be an island. Seamlessly tier or back up your data to public cloud providers while keeping your hot data local.
Core Storage Engine
Erasure Coding (8+4)
More resilient than RAID. We split data into 8 data shards and 4 parity shards. You can lose any 4 disks simultaneously and lose zero data.
Active Data Scrubber
Silent bit-rot is detected and healed automatically in the background. Your data integrity is constantly verified.
Disk Remapping
Gracefully handles disk path changes during replacement or migration without downtime.
Ready to Take Control of Your Data?
Explore CIDOS Enterprise for production environments, or start with Community Edition for evaluation — free forever.
The Privacy Manifesto
Last Updated: Dec 20, 2025 // v1.0
At CIDNIC, we believe that data is an extension of the self or the sovereign entity. It should not be mined, harvested, or held hostage.
1. No Vendor Lock-in
Your data should not be trapped in a proprietary format. CIDOS uses standard object storage paradigms and open API standards (S3). We prioritize portability: if you leave, your applications can continue to speak S3, and your data remains accessible through standard object workflows.
2. You Hold the Keys
We implement LocalKMS and Envelope Encryption. This means the master keys for your data reside on your infrastructure, under your control. When configured with customer-managed keys, CIDNIC does not possess the keys required to decrypt your data at rest. Support processes should not require access to your keys.
3. Zero Telemetry by Default
Modern software often "phones home." CIDOS is designed to run in air-gapped environments. CIDOS does not require telemetry to operate. Optional diagnostics can be enabled for support scenarios when you choose.
4. Accessible Technology
We are building a business, not a walled garden. Our community edition is free forever. Our enterprise features are paid, but our commitment to providing accessible, high-performance storage remains the bedrock of our innovation.
Questions about our stance?
We encourage security researchers and privacy advocates to audit our claims.
privacy@cidnic.comAPI Documentation
S3-compatible object storage APIs
CIDOS is designed to integrate with existing S3 tooling and applications. For detailed endpoint coverage, supported headers, and implementation notes, request the full documentation package.
What We Support
- Amazon S3-style APIs with SigV4 request signing
- Presigned URLs for time-bound access workflows
- Object Lock (WORM) retention patterns for immutable storage
- Encryption-at-rest options and TLS for data-in-transit
Need implementation guidance?
We can provide reference configurations, sizing guidance, and an integration walkthrough aligned to your tools.
About CIDNIC
Engineering-led infrastructure
CIDNIC builds private, S3-compatible object storage for organizations that need durability, security controls, and operational ownership. Our focus is practical engineering: predictable operations, clear integration paths, and security-first design.
Principles
- Portability: Integrate with standard S3 workflows to reduce lock-in risk.
- Sovereignty: Keep data and keys under your governance model.
- Resilience: Design for failure modes: disks fail, networks flap, workloads surge.
Want to talk architecture?
Share your workload goals and constraints—our team will propose a deployment model and sizing approach.
Terms of Service
Website & evaluation terms (summary)
This website is provided for informational purposes. Product, licensing, and support terms are defined in the applicable commercial agreement executed between CIDNIC and the customer.
Summary
- No warranties are made on this website content; specifications may change.
- Evaluation, licensing, and support obligations are governed by contract documents.
- Contact us to receive the current Terms for your procurement process.
Need the latest contractual Terms?
We can provide procurement-ready documents and respond to security/vendor questionnaires.
Service Level Agreement (SLA)
Support options (overview)
SLA terms vary by plan and are defined in the commercial agreement. We align support coverage, response targets, and escalation paths to your operational requirements.
Typical Inputs
- Coverage windows (business hours vs. 24x7)
- Severity definitions and response targets
- Escalation and communications plan
- Hardware replacement and spares model (appliances)
Want an SLA aligned to your operations?
We’ll map your environment and propose support coverage options for review.
Open Source Licenses
Third-party components used on this website
This website uses third-party open source libraries for styling and interactivity. Please refer to the upstream projects for license details.
Need a complete bill of materials?
We can provide a list of website dependencies and versions used in production.
Start the Conversation
We are driven by engineering excellence and a steadfast commitment to data sovereignty. Our solutions are architected for intelligence and resilience. Let's discuss your storage challenges.
Lab & HQ
123 Innovation Drive
Tech District, CA 94025
Direct Contact
engineering@cidnic.com
sales@cidnic.com
Resources
Documentation, support, and knowledge base
Documentation
Deployment guides, configuration reference, API documentation, and troubleshooting resources.
Enterprise Support
Severity-based response with escalation paths. Coverage options include business hours and 24x7 plans.
Contact Support
Reach our engineering team for deployment assistance, configuration questions, or product inquiries.
support@cidnic.comKnowledge Base
CIDOS Enterprise — Common Questions & Answers
for IT managers and decision-makers.
Understanding CIDOS
What is CIDOS Enterprise? Explain it simply.
CIDOS is a secure storage system for your company — much smarter and safer than a normal hard drive. It ensures nobody unauthorized can see your files (encryption), your files are safe even if drives break (erasure coding), you have a complete record of who touched what (audit trail), and your data stays on your own servers — not abroad.
It works like Amazon S3, so any software that works with S3 will work with CIDOS — no changes needed.
What does "S3-compatible" mean? Why should I care?
S3 is a standard way for software to store and retrieve files. Amazon created it, and now thousands of applications — from backup tools to ERPs to AI systems — speak S3.
When we say CIDOS is "S3-compatible," it means any software that works with Amazon S3 will work with CIDOS — no coding changes. Your developers don't need to learn anything new, and if you ever want to move, there's no lock-in.
In simple terms: It's like how any USB drive works with any laptop. S3 compatibility means any S3 application works with CIDOS.
Is CIDOS like Google Drive or Dropbox?
Not exactly. Google Drive and Dropbox are for personal use. CIDOS is for companies and organizations — it stores millions of files with enterprise-level security, encryption, and compliance features. Think of it as the storage engine behind your company's applications — ERP, websites, banking systems, hospital records.
Key difference: With Google Drive, your data sits on Google's servers outside Pakistan. With CIDOS, your data sits on YOUR servers, in YOUR office or data center.
Security & Ransomware Protection
How secure is CIDOS? Can hackers steal our data?
CIDOS has multiple layers of security:
- Encryption (AES-256-GCM): Every file is encrypted with military-grade standards.
- Access Control (IAM): Every user gets their own credentials. You control exactly who can see what.
- SigV4 Authentication: Every request is signed with a secure signature.
- MFA Support: Optional multi-factor authentication for extra security.
- Audit Trail: CIDOS logs everything — who accessed what, when, from which IP address.
- Credential Redaction: Passwords and secret keys are automatically hidden in logs.
What if ransomware attacks our servers?
Before an attack: Object Lock (WORM) makes important files undeletable. Least Privilege Access limits blast radius.
During an attack: Audit trails show exactly which files were accessed. Circuit Breaker limits abnormal operations.
After an attack: Auto-Healing rebuilds corrupted files from redundant copies. Version Rollback restores pre-attack state. Immutable backups survive because they simply cannot be modified.
Recovery time: Minutes to hours, not days or weeks.
Who controls the encryption keys? Can CIDNIC access our data?
YOU control the encryption keys. CIDOS gives you three options: Local KMS (keys on your server), AWS KMS, or HashiCorp Vault.
CIDNIC Systems does NOT have access to your data or encryption keys. The keys are generated and stored on YOUR infrastructure. We cannot see, read, or decrypt your data.
Can an employee delete everything accidentally or intentionally?
CIDOS has protections against both accidental and intentional deletion:
- Object Lock (Compliance Mode): Nobody can delete the file — not even the root admin — until the retention period expires.
- Object Lock (Governance Mode): Only specially authorized users can override the lock.
- Legal Hold: Indefinite lock on files related to legal cases.
- Versioning: "Deleted" files keep old versions — you can always restore.
- Audit Trail: Every deletion attempt is logged.
Data Sovereignty & Compliance
Our data must stay in Pakistan. Can CIDOS guarantee that?
Yes, 100%. CIDOS runs entirely on your own servers in Pakistan. Data stored in Pakistan, encryption keys in Pakistan, administration done from Pakistan, audit logs in Pakistan — no data sent abroad.
This makes you compliant with SBP data localization requirements, the Personal Data Protection Bill, and internal data residency policies.
Does CIDOS help with SBP (State Bank) compliance?
Yes. CIDOS addresses key SBP requirements: data resides in Pakistan on local servers, AES-256 encryption at rest and in transit, full IAM with 25+ audit event types, Object Lock for record retention (1-year, 7-year, etc.), and security incident detection via comprehensive audit trails.
Compliance evidence is recorded automatically, 24/7 — no manual collection before inspections.
Does CIDOS need internet to work?
No. After initial one-time license activation, CIDOS works 100% without internet. This is critical for organizations with unreliable internet, restricted networks, air-gapped environments, or locations affected by connectivity disruptions.
Cost, Licensing & Integration
How much does CIDOS cost compared to cloud storage?
For 100 TB, cloud storage can cost $37,000–$52,000 annually (storage + API + egress fees). CIDOS Enterprise is a one-time license plus locally procured hardware — no monthly bills in USD, no egress fees, no API fees. Most organizations recover their investment within 6–12 months.
What is the licensing model? Do we pay monthly?
Simple and transparent: one-time license per machine with lifetime validity. No monthly subscriptions, no per-GB charges, no per-request charges, no egress fees. Everything is included — encryption, audit, monitoring.
For evaluation: Developer mode (all features, no license) and Trial mode (limited features, no cost) let you test before buying.
Will CIDOS work with our existing software?
If your software works with Amazon S3, it works with CIDOS — no changes needed. This includes backup tools (Veeam, Commvault, Rclone), ERP systems (SAP, Oracle), database backups, DevOps tools (AWS CLI, boto3), file browsers (S3 Browser, Cyberduck), medical imaging (PACS/DICOM), data analytics (Spark, Jupyter), and AI/ML tools (TensorFlow, PyTorch).
Connection is simple: point your S3 endpoint URL to your CIDOS server — typically a 1-line configuration change.
Reliability & Getting Started
What happens if a hard drive fails?
Nothing visible happens to your users — applications continue normally. CIDOS stores data across 12 disks using erasure coding (8 data + 4 parity). Even if 4 disks fail simultaneously, your data is 100% safe and accessible. When you replace a failed disk, CIDOS automatically detects the new disk and rebuilds all missing data — no manual intervention needed.
How long does it take to set up CIDOS?
Quick evaluation: 30 minutes. Development/staging: 15 minutes. Production single-server (12 disks, encryption, full config): 2–4 hours. Multi-server cluster: 1 day.
CIDOS is just two files (server binary and CLI tool) plus one configuration file. No complex multi-component installation.
Why should my company use CIDOS instead of cloud storage?
Six key reasons:
- Your data stays in your hands — on your servers, in your building, not abroad.
- Ransomware protection — locked files cannot be deleted or encrypted by attackers.
- Cost savings — one-time license, no monthly bills, no egress or API fees.
- Works without internet — critical advantage during connectivity disruptions.
- Regulatory compliance — automatic audit trails for SBP, SECP, and other regulators.
- No vendor dependency — you own the hardware and software license.
Still have questions?
Our team is ready to help. Get answers tailored to your industry and use case.
Careers at CIDNIC
Join the team building sovereign storage infrastructure
We're looking for driven professionals who want to make an impact in enterprise data infrastructure. If you're passionate about technology and sales, we want to hear from you.
Sales Executive — CIDOS Enterprise
About the Role
We're hiring a Sales Executive to drive adoption of CIDOS Enterprise — our flagship S3-compatible, sovereign object storage platform. You'll work directly with enterprise IT teams, CIOs, and procurement leaders across banking, healthcare, government, and manufacturing sectors in Pakistan. This is a high-impact role where you'll own the full sales cycle — from initial outreach and solution discovery through POC coordination to deal closure.
Key Responsibilities
- Identify and develop enterprise accounts for CIDOS Enterprise storage solutions
- Conduct discovery meetings to align CIDOS capabilities with customer storage, compliance, and sovereignty requirements
- Coordinate proof-of-concept deployments and technical evaluations with the engineering team
- Develop proposals, handle pricing discussions, and manage the deal pipeline
- Build and maintain relationships with channel partners and system integrators
Requirements
- 2+ years of B2B technology sales experience (storage, infrastructure, or enterprise software preferred)
- Understanding of enterprise IT environments — storage, networking, security, and compliance
- Excellent communication skills — ability to present to technical and executive audiences
- Self-motivated with a track record of meeting or exceeding sales targets
- Willingness to travel for customer visits across Pakistan
Don't see a match?
We're always interested in hearing from talented people. Send us your resume and let us know how you'd contribute.
Our Partners
Authorized CIDOS Enterprise sales partners
CIDNIC works with trusted technology partners to deliver CIDOS Enterprise storage solutions to organizations across Pakistan. Our partners provide local sales, deployment, and integration services.
SSBACHA Technologies
ssbacha.netAuthorized sales partner for CIDOS Enterprise in Pakistan. Delivers comprehensive IT solutions, GIS Solutions, Custom Softwares for government, and large enterprise customers.
CIDOS Enterprise Sales PartnerArabLine Computers
ArabLine ComputersAuthorized sales partner for CIDOS Enterprise. Provides end-to-end IT solutions including server hardware, networking, and storage infrastructure for mid-size and enterprise organizations across Pakistan.
CIDOS Enterprise Sales PartnerCIDOS Enterprise Partner Program
Join the CIDNIC partner ecosystem to deliver sovereign, enterprise-grade storage solutions to your customers.
System Integrators
Deploy CIDOS Enterprise as part of your infrastructure solutions. Offer deployment, configuration, and managed services to enterprise customers.
Value-Added Resellers
Bundle CIDOS with hardware solutions for turnkey storage appliances. Offer pre-configured, enterprise-ready storage to your customer base.
Technology Partners
Integrate CIDOS into your software platform as the storage backend. Offer S3-compatible storage with sovereignty controls to your end users.
Architecture guidance, deployment support, and technical training for your team.
Approved collateral, co-branded materials, and joint go-to-market strategies.
Structured deal registration process with margin protection for qualified opportunities.
Dedicated partner support with severity-based response SLAs and escalation paths.